The Atbash cipher is one of the simplest and oldest known substitution ciphers. Its rule is almost stark in its elegance: take the alphabet, reverse it, and replace each letter with the letter directly opposite it.
So:
| Plain | Cipher |
|---|---|
A |
Z |
B |
Y |
C |
X |
D |
W |
E |
V |
... |
... |
Z |
A |
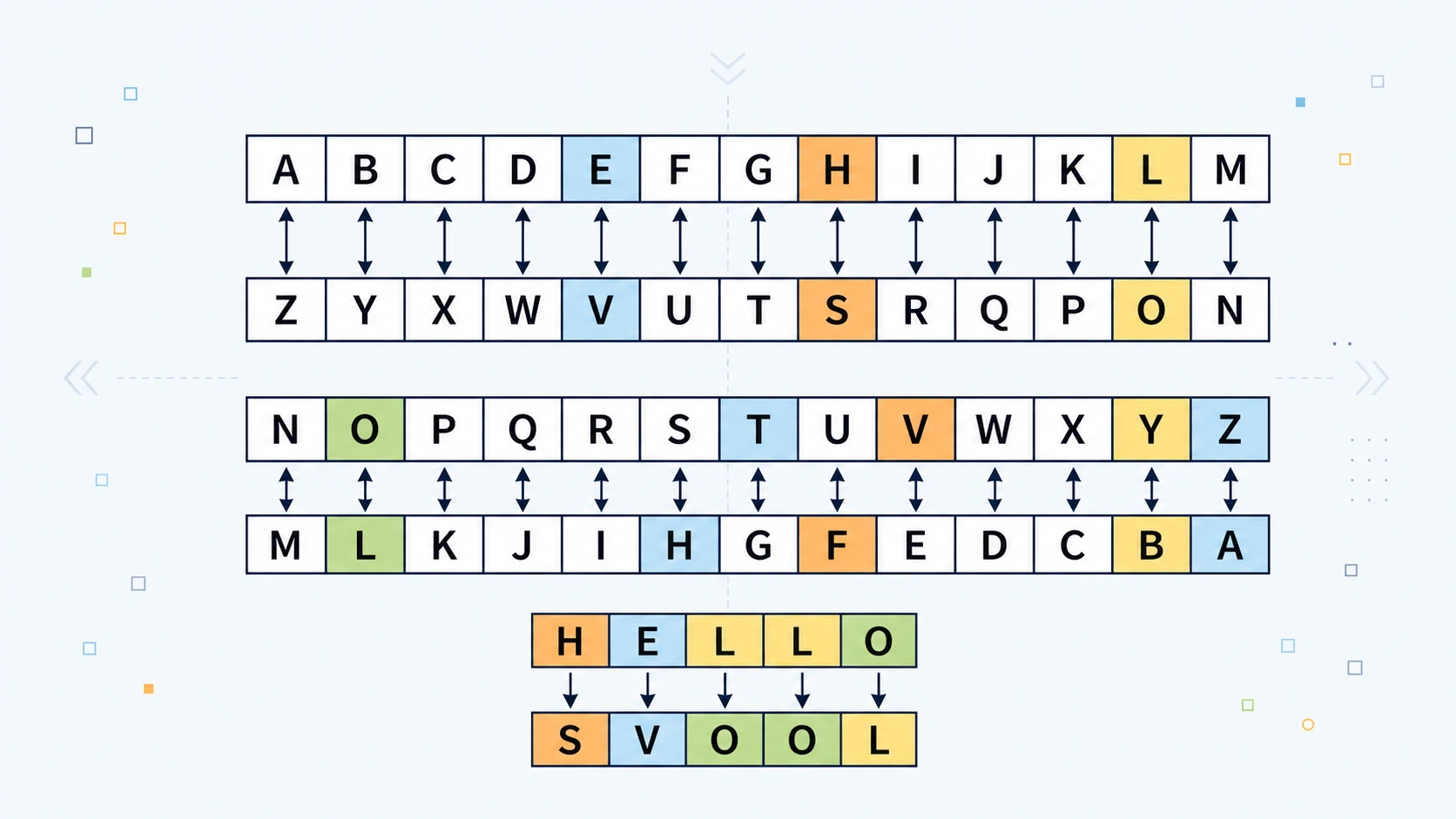
Under Atbash, the beginning of the alphabet is exchanged with the end. A becomes Z. B becomes Y. C becomes X. The alphabet is not shifted, scrambled, or keyed. It is simply folded back on itself.
For example:
HELLO -> SVOOL
The transformation looks strange at first, but the rule behind it is completely regular. Each letter is replaced by its mirror partner.
That makes Atbash an unusually clean cipher. It has no secret keyword, no changing alphabet, no numerical key, and no complicated table. Once the reversed alphabet is known, the whole system is known.
This is both its charm and its fatal weakness.
Atbash is often introduced as a beginner cipher, but historically it is more than just a classroom trick. It was originally associated with the Hebrew alphabet. Examples of Atbash are traditionally identified in the Book of Jeremiah, and the name itself comes from the pairing of Hebrew letters: aleph with taw, and beth with shin: the first with the last, the second with the second-last. That pairing gives the name Atbash: A-T-B-Sh.
In modern English form, Atbash is usually written using the Latin alphabet:
Plain: ABCDEFGHIJKLMNOPQRSTUVWXYZ
Cipher: ZYXWVUTSRQPONMLKJIHGFEDCBA
That table is the entire cipher.
If the plaintext is:
THE SECRET IS HIDDEN
then the Atbash ciphertext becomes:
GSV HVXIVG RH SRWWVM
It looks cryptic. It feels like a secret message. But the moment someone recognises the reversal pattern, the concealment disappears.
This is the central lesson of Atbash. It shows how easily writing can be transformed into something unfamiliar, but also how little that transformation means if there is no hidden key.
Like A1Z26, Atbash is valuable not because it is strong, but because it makes the mechanics of substitution almost impossible to miss.
Atbash is the alphabet in a mirror.
That is the whole idea.
And because the idea is so pure, it remains one of the best entry points into classical cryptography.
Atbash at a Glance
| Feature | Atbash Cipher |
|---|---|
| Cipher type | Monoalphabetic substitution cipher |
| Main rule | Reverse the alphabet |
| Standard English mapping | A <-> Z, B <-> Y, C <-> X |
| Example | HELLO -> SVOOL |
| Key | No user-chosen secret key in standard Atbash |
| Decryption | Same as encryption |
| Security level | Extremely weak |
| Best use | Learning, puzzles, demonstrations, simple obfuscation |
Atbash is simple enough to understand in seconds, but it teaches several important ideas at once: substitution, reversibility, symmetry, pattern leakage, and the difference between making text unreadable and making it genuinely secure.
The Mirror Rule: How Atbash Works
Atbash works by pairing each letter with the letter in the opposite position of the alphabet.
In the English alphabet, there are 26 letters. The first letter pairs with the twenty-sixth, the second with the twenty-fifth, the third with the twenty-fourth, and so on.
So the basic pairs are:
The second half of the alphabet simply reverses the same pairings.
This gives Atbash an important property: the same operation encrypts and decrypts.
If A becomes Z, then Z becomes A. If H becomes S, then S becomes H. If M becomes N, then N becomes M.
So if you apply Atbash once, you hide the message. If you apply Atbash a second time, you get the original message back.
For example:
HELLO -> SVOOL
SVOOL -> HELLO
That is not a coincidence. It is built into the symmetry of the cipher.
This makes Atbash a self-inverse cipher. In plain language, that means the cipher reverses itself. You do not need a separate decryption method. The encryption rule and decryption rule are identical.
Take the word:
CIPHER
Convert each letter using the reversed alphabet:
| Plain letter | C |
I |
P |
H |
E |
R |
|---|---|---|---|---|---|---|
| Atbash pair | X |
R |
K |
S |
V |
I |
So:
CIPHER -> XRKSVI
Now apply the same rule again:
| Cipher letter | X |
R |
K |
S |
V |
I |
|---|---|---|---|---|---|---|
| Atbash pair | C |
I |
P |
H |
E |
R |
So:
XRKSVI -> CIPHER
That is the mechanical heart of Atbash.
It is not random. It is not arbitrary. It is a perfectly regular reflection.
Atbash as Gentle Mathematics
Atbash can be explained without mathematics, but a little arithmetic reveals why it behaves so neatly.
Number the English alphabet from 0 to 25:
| Letter | Number |
|---|---|
A |
0 |
B |
1 |
C |
2 |
... |
... |
Y |
24 |
Z |
25 |
In this numbering system, Atbash sends each number to:
$$ 25 - x $$
where x is the position of the plaintext letter.
| Letter | Number | Atbash calculation | Result |
|---|---|---|---|
A |
0 |
25 - 0 = 25 |
Z |
B |
1 |
25 - 1 = 24 |
Y |
C |
2 |
25 - 2 = 23 |
X |
M |
12 |
25 - 12 = 13 |
N |
Z |
25 |
25 - 25 = 0 |
A |
This one-line formula captures the whole cipher:
$$ \operatorname{Atbash}(x) = 25 - x $$
The reason Atbash decrypts itself is also visible here. If you apply the formula twice, you get back where you started.
First application:
$$ x \rightarrow 25 - x $$
Second application:
$$ 25 - (25 - x) $$
Now simplify:
$$ 25 - 25 + x = x $$
So after two Atbash transformations, the original letter returns.
That is the higher-level structure of the cipher. Atbash is not merely a lookup table. It is a reflection across the centre of the alphabet.
In the language of classical cryptography, Atbash is a type of monoalphabetic substitution cipher. A monoalphabetic substitution replaces each plaintext letter with one fixed ciphertext symbol throughout the message.
Atbash fits that definition exactly.
Every A becomes Z. Every B becomes Y. Every C becomes X. The mapping never changes.
Atbash can also be described as a special case of the Affine cipher. In the usual 0 to 25 alphabet numbering, the Affine cipher has the form:
$$ E(x) = ax + b \pmod{26} $$
For Atbash, the rule is:
$$ E(x) = 25 - x \pmod{26} $$
This can also be written as:
$$ E(x) = -x + 25 \pmod{26} $$
In Affine form, that means:
a = 25
b = 25
So Atbash can be written as:
$$ E(x) = 25x + 25 \pmod{26} $$
This may sound more advanced than Atbash needs, but it shows something useful: even the simplest classical ciphers can often be placed inside a larger mathematical family.
Atbash is not mathematically deep, but it is mathematically tidy.
It is symmetry turned into encryption.
The Key That Is Not Really a Key
Most ciphers have a key: some piece of information that controls the encryption.
The Caesar cipher has a shift value. ROT13 uses a shift of 13. The Vigenere cipher uses a keyword. The Playfair cipher uses a keyword square. The Hill cipher uses a matrix.
Standard Atbash has no user-chosen secret key.
Once the alphabet is known, the substitution is completely determined.
There is only one standard Atbash alphabet for English:
Plain: ABCDEFGHIJKLMNOPQRSTUVWXYZ
Cipher: ZYXWVUTSRQPONMLKJIHGFEDCBA
Once an attacker suspects Atbash, there is nothing left to discover.
This is why Atbash is best understood as a historical cipher and a form of simple obfuscation, not as secure encryption. It transforms the message, but it does not provide meaningful key-based secrecy.
That distinction matters.
A transformation is not automatically secure just because it makes text unreadable at first glance. For secrecy, the attacker must be missing something important. In Atbash, the attacker is missing very little. They only need to recognise the pattern.
Still, this absence of a key is also part of why Atbash is educationally useful. It lets the reader focus on the pure idea of substitution before adding the extra complexity of keys, shifting alphabets, polyalphabetic rules, or modular arithmetic.
Atbash is not where cryptography ends.
It is where the basic grammar of substitution becomes visible.
A Worked Example: Encrypting a Message
Let the plaintext be:
MEET AT DAWN
Using Atbash, convert each letter into its opposite.
First word:
| Plain letter | M |
E |
E |
T |
|---|---|---|---|---|
| Atbash pair | N |
V |
V |
G |
So:
MEET -> NVVG
Second word:
| Plain letter | A |
T |
|---|---|---|
| Atbash pair | Z |
G |
So:
AT -> ZG
Third word:
| Plain letter | D |
A |
W |
N |
|---|---|---|---|---|
| Atbash pair | W |
Z |
D |
M |
So:
DAWN -> WZDM
Put together:
MEET AT DAWN -> NVVG ZG WZDM
The message is transformed, but its structure remains quite visible.
There are still three words. The first word still has four letters. The second word still has two letters. The third word still has four letters.
Repeated letters remain repeated. The two Es in MEET become two Vs in NVVG. The repeated A in the full phrase becomes repeated Z.
This is one reason Atbash is easy to attack. It hides the letters, but it does not hide much of the pattern.
Now decrypt the ciphertext:
NVVG ZG WZDM
Apply the same Atbash rule again.
| Cipher letter | N |
V |
V |
G |
|---|---|---|---|---|
| Atbash pair | M |
E |
E |
T |
So:
NVVG -> MEET
Then:
| Cipher letter | Z |
G |
|---|---|---|
| Atbash pair | A |
T |
So:
ZG -> AT
Then:
| Cipher letter | W |
Z |
D |
M |
|---|---|---|---|---|
| Atbash pair | D |
A |
W |
N |
So:
WZDM -> DAWN
Recovered message:
MEET AT DAWN
The same table performs both operations. That is one of the most satisfying features of Atbash: the cipher is its own undoing.
Atbash and the Hebrew Alphabet
The historical Atbash cipher is most closely associated with the Hebrew alphabet, not the modern English alphabet.
In Hebrew form, the first letter aleph is paired with the last letter taw. The second letter beth is paired with shin. These pairings give the name Atbash: aleph-taw, beth-shin.
This is important because Atbash is sometimes casually presented as if it began as an English A-Z trick. That is misleading. The English version is a later adaptation of a more general alphabet-reversal idea. The principle works with any ordered alphabet, but the historical name and famous early examples belong to Hebrew.
In the Hebrew Bible, Atbash is traditionally identified in several passages in the Book of Jeremiah. A University College London Hebrew worksheet notes Atbash in Jeremiah 25:26, 51:1, and 51:41, while also cautioning that it is unclear whether the cipher was being used for concealment from enemies or as a literary device.
The most famous example is often given as the transformation of Babel, or Babylon, into Sheshach. The details depend on the Hebrew letters rather than English spelling, but the principle is the same: letters are replaced with their opposite partners in the Hebrew alphabet.
That point deserves care.
Atbash was not necessarily "encryption" in the modern security sense. In a biblical or literary context, it may have worked as wordplay, symbolic reversal, veiled naming, rhetorical device, limited concealment, or some mixture of these.
Modern cryptography is usually concerned with adversaries, keys, algorithms, authentication, randomness, and formal security assumptions. Ancient textual uses may have had broader literary and cultural purposes.
So the safest historical statement is this:
Atbash is an ancient alphabet-reversal substitution system associated with the Hebrew alphabet, and examples of it are traditionally recognised in Jeremiah. Its exact function in those passages is not completely certain.
That makes it historically richer than many toy ciphers.
Atbash is not just a puzzle-book invention. It is a very old demonstration of how ordered writing systems can be manipulated into hidden or symbolic forms.
Why a Reversed Alphabet Was Useful
Atbash is weak by modern standards, but it was not pointless.
In a world without computers, databases, search engines, automated frequency analysis, or standardised puzzle conventions, even a simple transformation could create a useful barrier. If a reader did not know the reversal rule, the message might look strange enough to delay recognition.
Atbash also has several practical advantages.
First, it is easy to memorise. You do not need a written key. You only need to know that the alphabet is reversed. This makes it convenient for quick mental encoding.
Second, it is symmetrical. The same method encrypts and decrypts. That reduces the chance of procedural mistakes.
Third, it preserves alphabetic form. Unlike A1Z26, which turns letters into numbers, Atbash keeps the message as letters. That makes it more compact and easier to write in ordinary text.
Fourth, it has a strong visual idea behind it. The alphabet is turned around. This makes the cipher memorable.
In casual use, those strengths matter. A cipher used in a puzzle, classroom, game, private note, or symbolic text does not always need real security. Sometimes it only needs to create distance from plain reading.
Atbash does that well.
Consider:
THE GATE IS OPEN
Atbash gives:
GSV TZGV RH LKVM
To someone familiar with classical ciphers, this is easy. But to a casual reader, it may be just obscure enough to feel hidden.
That is the level at which Atbash works: not as a serious lock, but as a screen.
It disguises, but it does not truly protect.
The Cipher's Main Weaknesses
Atbash has several weaknesses, and they are severe.
It Has No Secret Key
This is the fundamental problem.
There is only one standard Atbash mapping for a given alphabet. Once the attacker recognises the method, the entire cipher is solved.
A Caesar cipher at least has 25 possible non-trivial shifts in English. That is still tiny, but it gives the attacker something to test. Atbash has no equivalent keyspace. The rule is fixed.
It Preserves Letter Frequency
Atbash is monoalphabetic. That means every plaintext letter always becomes the same ciphertext letter.
In English, E is common. Under Atbash, E becomes V. So V will often be common in the ciphertext.
T becomes G. A becomes Z. O becomes L.
The frequencies are renamed, but not flattened.
A long Atbash message still carries the statistical fingerprint of English. The most common letters are still common; they are merely wearing different labels.
This is a general weakness of monoalphabetic substitution. Britannica explains that monoalphabetic substitution preserves the frequency distribution of the plaintext symbols, only relabelled in the ciphertext.
It Preserves Word Shapes
If spaces are left intact, word lengths remain visible.
A one-letter word remains a one-letter word. A three-letter repeated word remains a repeated three-letter pattern.
For example:
THE -> GSV
Because THE is so common in English, GSV becomes a strong clue. In fact, GSV is one of the classic giveaways of Atbash.
Similarly:
| Plaintext | Atbash |
|---|---|
THE |
GSV |
AND |
ZMW |
YOU |
BLF |
OF |
LU |
TO |
GL |
IS |
RH |
Common words create recognisable shadows.
It Preserves Repetition
Repeated plaintext letters become repeated ciphertext letters.
For example:
BALLOON -> YZOOLLM
The double L becomes double O. The double O becomes double L.
Patterns like this are valuable to an attacker because they reveal internal structure even before the message is fully solved.
It Is Easy to Recognise
Atbash has a distinctive look. Certain ciphertext fragments are especially suspicious.
| Ciphertext clue | Likely plaintext |
|---|---|
GSV |
THE |
ZMW |
AND |
BLF |
YOU |
RH |
IS |
GL |
TO |
SVOOL |
HELLO |
Once someone has seen Atbash a few times, these fragments become almost as recognisable as fingerprints.
It Gives a False Sense of Security
This may be its most important weakness from an educational point of view.
Atbash looks like encryption. It produces unfamiliar text. It feels secret. But its security is extremely thin.
That makes it useful as a warning.
It teaches that unreadable is not the same as secure.
A message can be transformed, disguised, stylised, and still be trivial to recover.
How Atbash Is Broken
Breaking Atbash usually does not require advanced cryptanalysis. It often requires recognition.
Suppose an attacker sees:
GSV JFRXP YILDM ULC QFNKH LEVI GSV OZAB WLT
A few features stand out.
The first word is GSV.
In beginner cryptography, GSV is a famous Atbash form of THE:
| Ciphertext | G |
S |
V |
|---|---|---|---|
| Plaintext | T |
H |
E |
Once that is spotted, the rest of the message can be decoded by reversing the alphabet.
The full plaintext is:
THE QUICK BROWN FOX JUMPS OVER THE LAZY DOG
This is not really "cracked" in the dramatic sense. It is recognised and reversed.
For longer texts, an attacker can use frequency analysis. Since Atbash is a monoalphabetic substitution cipher, the frequency pattern of the plaintext language survives.
In ordinary English, the most common letters are often E, T, A, O, I, N, S, H, and R, although exact order varies by text.
In Atbash, those letters become:
| Common plaintext letter | Atbash form |
|---|---|
E |
V |
T |
G |
A |
Z |
O |
L |
I |
R |
N |
M |
S |
H |
H |
S |
R |
I |
So if a ciphertext has many Vs, Gs, Zs, Ls, Rs, and Ms, Atbash becomes a reasonable guess.
But frequency analysis is often unnecessary. Atbash is so simple and so well known that an attacker will usually test it early, especially if the ciphertext consists only of letters and retains word spaces.
A practical attack goes like this:
- Look for common Atbash giveaways such as
GSV,ZMW,BLF,RH, orGL. - Reverse the alphabet and test whether the result becomes readable.
- If the output is coherent English, the cipher is solved.
- If not, move on to Caesar, ROT13, general substitution, Vigenere, or other likely candidates.
This is why Atbash provides almost no resistance against anyone with even basic cipher knowledge.
Its weakness is not subtle.
The reversed alphabet is too regular, too standard, and too easily tested.
Why Atbash Still Looks Good in Puzzles
Despite its weakness, Atbash remains popular in puzzles, games, escape rooms, classroom activities, and online cipher tools.
That is because puzzle ciphers are not judged only by cryptographic strength. They are also judged by elegance, recognisability, solvability, and satisfaction.
Atbash performs well on those terms.
It gives the solver a genuine "click" moment. At first, the text looks strange. Then the reversal is noticed. Suddenly, the whole message opens.
That moment is satisfying because the rule is simple but not invisible. It sits at the right level for beginner puzzle design: not random, not too hard, but not completely obvious to someone who has never seen it.
Atbash also has a neat aesthetic. A reversed alphabet feels like a hidden symmetry. It is easy to explain visually and easy to remember.
This makes it useful for:
- introductory cryptography lessons
- puzzle hunts
- escape-room clues
- children's secret messages
- hobby cipher tools
- codebreaking warm-ups
- demonstrations of monoalphabetic substitution
- programming exercises
It is not a secure cipher, but it is an excellent teaching cipher.
That distinction is important. A weak cipher can still be intellectually useful if it reveals the right concept clearly.
Atbash reveals substitution, symmetry, reversibility, monoalphabetic weakness, frequency preservation, and the difference between disguise and security.
That is a lot of value for a cipher with one rule.
Atbash Compared with Other Ciphers
Atbash sits near several other classical systems. Comparing them helps clarify its role.
Atbash vs Caesar Cipher
The Caesar cipher shifts the alphabet by a fixed number of positions.
With a shift of 3:
| Plain | Cipher |
|---|---|
A |
D |
B |
E |
C |
F |
Atbash does not shift the alphabet. It reverses it.
Caesar is controlled by a numerical key. Atbash usually has no user-chosen key.
So Caesar is only slightly more flexible, but conceptually different. Caesar moves the alphabet around a wheel. Atbash flips it like a mirror.
Atbash vs ROT13
ROT13 is a Caesar cipher with a shift of 13. Like Atbash, it is self-inverse: applying ROT13 twice returns the original message.
ROT13:
HELLO -> URYYB
URYYB -> HELLO
Atbash:
HELLO -> SVOOL
SVOOL -> HELLO
Both are weak. Both are useful for casual obfuscation. Both teach reversibility very clearly.
The difference is that ROT13 rotates the alphabet halfway around, while Atbash reflects it.
Atbash vs A1Z26
A1Z26 replaces letters with their alphabet positions:
| Letter | Number |
|---|---|
A |
1 |
B |
2 |
C |
3 |
Atbash keeps the output as letters, while A1Z26 changes letters into numbers.
The two systems are different in appearance, but both rely on the ordered alphabet. A1Z26 writes the order directly. Atbash reverses the order.
Atbash vs Affine Cipher
The Affine cipher treats letters as numbers and applies a mathematical formula.
Atbash can be seen as a special Affine transformation because it maps each position x to 25 - x in the English alphabet.
That makes Atbash a useful stepping stone toward mathematical cryptography. It shows how letter substitution can be described with arithmetic rather than only with lookup tables.
Atbash vs General Monoalphabetic Substitution
In a general monoalphabetic substitution cipher, the alphabet may be scrambled in many possible ways.
For example:
| Plain | Cipher |
|---|---|
A |
Q |
B |
M |
C |
X |
D |
A |
Atbash is a very special monoalphabetic substitution because the substitution alphabet is not arbitrary. It is the exact reverse of the plaintext alphabet.
That makes Atbash easier to memorise, but also easier to recognise.
Atbash vs Vigenere Cipher
The Vigenere cipher uses a changing sequence of Caesar shifts controlled by a keyword. Unlike Atbash, the same plaintext letter can encrypt to different ciphertext letters depending on its position.
That makes Vigenere much stronger than Atbash against simple frequency analysis, although it too can be broken if used carelessly or with short repeated keys.
Atbash is monoalphabetic.
Vigenere is polyalphabetic.
That distinction marks one of the major steps forward in classical cryptography.
Atbash in the Modern World
Atbash has no serious role in modern secure communication. It should not be used to protect passwords, private messages, financial data, personal information, API keys, recovery phrases, or anything else that actually matters.
Modern encryption uses carefully analysed algorithms, secret keys, authentication, randomness, and formal security assumptions.
Atbash has none of those.
But it still matters.
It matters because it teaches the difference between transformation and security.
A beginner can look at Atbash and see a message become unreadable. Then they can learn how quickly that unreadability collapses. That is a valuable lesson. Many bad security systems fail in exactly this way: they make data look different while offering little real resistance to attack.
Atbash also matters because it shows that letters can be treated as positions in a structured system. Once that idea is understood, the path opens toward Caesar shifts, modular arithmetic, Affine ciphers, Vigenere tables, frequency analysis, and eventually modern cryptographic thinking.
There is also a programming reason to keep Atbash around. It is an ideal first cipher to implement in code. The rules are simple, but the practical details still matter:
- Should spaces be preserved?
- Should punctuation be left unchanged?
- Should case be preserved?
- Should non-English letters be ignored?
- Should digits be transformed or passed through?
- Should the function handle lowercase input?
- Should the tool warn users that Atbash is not secure encryption?
These are small questions, but they are the same kind of questions programmers face when turning any clean idea into a usable tool.
Atbash is therefore useful in three different ways:
- as a historical cipher
- as a puzzle cipher
- as a programming exercise
Its security is weak, but its teaching value is strong.
The Real Lesson of Atbash
Atbash is not impressive because it is difficult.
It is impressive because it is so clear.
It takes one of the most basic structures in writing, alphabetic order, and turns it into a reversible system. The first letter becomes the last. The second becomes the second-last. The alphabet becomes its own mirror.
That simple act contains several important ideas.
A message can be transformed.
A transformation can be reversed.
A rule can be simple enough to memorise.
A cipher can look secret without being secure.
A fixed substitution preserves patterns.
A system with no secret key cannot provide serious protection.
Those ideas sit close to the foundation of classical cryptography. Atbash is not a destination, but it is a beautiful starting point.
It also has a kind of historical dignity. Unlike many beginner ciphers invented merely for school exercises, Atbash reaches back into ancient textual tradition. Its association with Hebrew writing and the Book of Jeremiah gives it a deeper cultural presence than its simplicity might suggest.
The precise purpose of those ancient uses may not be fully settled, but the cipher itself remains a striking example of symbolic reversal.
In the end, Atbash is best understood as a mirror cipher: elegant, ancient, memorable, and weak.
It does not protect secrets from serious attackers.
But it does reveal one of the oldest instincts in cryptography: take the familiar symbols of language, transform them by rule, and make the reader work to bring them back.
A Small Python Example
Atbash is particularly easy to implement in Python because each letter has exactly one partner.
The simplest version reads through the text one character at a time. If the character is an English letter from A to Z or a to z, it replaces it with the corresponding reversed-alphabet letter. If the character is not an English letter, such as a space, punctuation mark, digit, symbol, or non-English character, it leaves it unchanged.
Python exampleShow code
def atbash(text):
result = []
for char in text:
if 'A' <= char <= 'Z':
mirrored = chr(ord('Z') - (ord(char) - ord('A')))
result.append(mirrored)
elif 'a' <= char <= 'z':
mirrored = chr(ord('z') - (ord(char) - ord('a')))
result.append(mirrored)
else:
result.append(char)
return ''.join(result)
message = "Meet at dawn!"
encrypted = atbash(message)
decrypted = atbash(encrypted)
print("Plaintext :", message)
print("Encrypted :", encrypted)
print("Decrypted :", decrypted)
Expected output:
Plaintext : Meet at dawn!
Encrypted : Nvvg zg wzdm!
Decrypted : Meet at dawn!
The key line in the uppercase branch is:
mirrored = chr(ord('Z') - (ord(char) - ord('A')))
This calculates how far the character is from the start of the alphabet, then subtracts that distance from the end of the alphabet.
For example, with uppercase C:
C is two letters after A.
So the mirrored letter is two letters before Z.
That gives X.
The lowercase branch does the same thing using lowercase a and z.
This version preserves punctuation and spacing, which is usually what users expect from an Atbash tool. So:
Hello, world!
becomes:
Svool, dliow!
The comma, space, and exclamation mark are not encrypted. They remain where they are.
That is convenient, but it also reminds us of a cryptographic weakness. Preserving spaces and punctuation makes the output easier to read, but it also gives an attacker more structure. Word lengths, sentence shape, and punctuation patterns all survive.
A more compact version can be written using Python's translation table tools:
import string
def atbash(text):
plain = string.ascii_uppercase + string.ascii_lowercase
cipher = string.ascii_uppercase[::-1] + string.ascii_lowercase[::-1]
table = str.maketrans(plain, cipher)
return text.translate(table)
message = "The secret is hidden."
encrypted = atbash(message)
decrypted = atbash(encrypted)
print("Plaintext :", message)
print("Encrypted :", encrypted)
print("Decrypted :", decrypted)
Expected output:
Plaintext : The secret is hidden.
Encrypted : Gsv hvxivg rh srwwvm.
Decrypted : The secret is hidden.
This second version is shorter because str.maketrans() builds the substitution table directly.
The expression:
string.ascii_uppercase[::-1]
means "take the uppercase alphabet and reverse it."
So:
ABCDEFGHIJKLMNOPQRSTUVWXYZ
becomes:
ZYXWVUTSRQPONMLKJIHGFEDCBA
That is exactly Atbash.
The nice thing about this implementation is that it mirrors the conceptual structure of the cipher. Atbash is just a reversed alphabet, and the code literally creates a reversed alphabet.
As a programming exercise, Atbash is small but useful. It teaches character-by-character processing, alphabet mapping, case handling, punctuation preservation, and reversible transformation. It is also a good first example of how a cipher can be expressed both as a lookup table and as a mathematical rule.
The code is easy.
The lesson is bigger:
changing text is not the same as securing it.