Most early ciphers are easy to explain because they repeat the same trick from start to finish. A Caesar cipher shifts every letter by a fixed amount. An affine cipher applies one substitution rule all the way through. A keyword cipher may scramble the alphabet, but it still uses only one substitution alphabet for the whole message. The weakness is always the same: the structure of the language survives. The same plaintext letter keeps turning into the same ciphertext letter, so letter frequencies, common pairings, and repeated patterns still leak through. The great step forward in the Vigenère cipher was to stop relying on one alphabet and begin rotating among several.
The Vigenère cipher is the best-known example of a polyalphabetic substitution cipher. Instead of using one substitution alphabet throughout, it uses a sequence of Caesar-style shifts controlled by a keyword. That single change makes a major difference. In a monoalphabetic cipher, every E is encrypted the same way. In a Vigenère cipher, one E may become X, another J, another P, depending on which letter of the key is active at that position. That is why the cipher once acquired an almost legendary reputation and why it occupies such an important place in the history of cryptography.
The central idea
At heart, the Vigenère cipher is just a repeated series of Caesar ciphers. You choose a keyword, write it repeatedly above the plaintext, and let each key letter determine the shift for the matching plaintext letter. If the key letter is A, the shift is 0. If it is B, the shift is 1. If it is K, the shift is 10. Then everything wraps around modulo 26.
There are two common ways to picture the process. The traditional classroom method uses the Vigenère square, also called the tabula recta: a grid of 26 shifted alphabets. One axis gives the plaintext letter, the other gives the key letter, and their intersection gives the ciphertext. The cleaner mathematical version is even simpler: convert letters to numbers with A = 0 through Z = 25, add plaintext and key values modulo 26, and convert back to letters. These are not two different systems. They are the same cipher described in two different languages.
What the key really is
The square itself is not the secret. It is only the mechanism. The real secret is the keyword or key phrase shared by sender and receiver. That practical detail mattered historically. A person could remember a word or short phrase much more easily than they could carry around a large secret chart. Even if an enemy understood the general method, the system could still hold as long as the key remained unknown.
Classical presentations usually remove spaces and punctuation, reduce everything to one alphabetic stream, and often group the result into blocks of five letters. Modern teaching versions often preserve spaces and punctuation for readability, but the underlying rule is the same: only letters actually take part in encipherment.
In plain language, the operating procedure is simple:
- Choose a keyword.
- Repeat it until it matches the message length.
- Turn each key letter into a shift from
0to25. - Shift each plaintext letter by the amount given by its matching key letter.
- Wrap around the alphabet when necessary.
The cleverness lies not in complication, but in variation. The substitution rule keeps changing as the message moves forward.
A simple worked example
Let us encrypt the message:
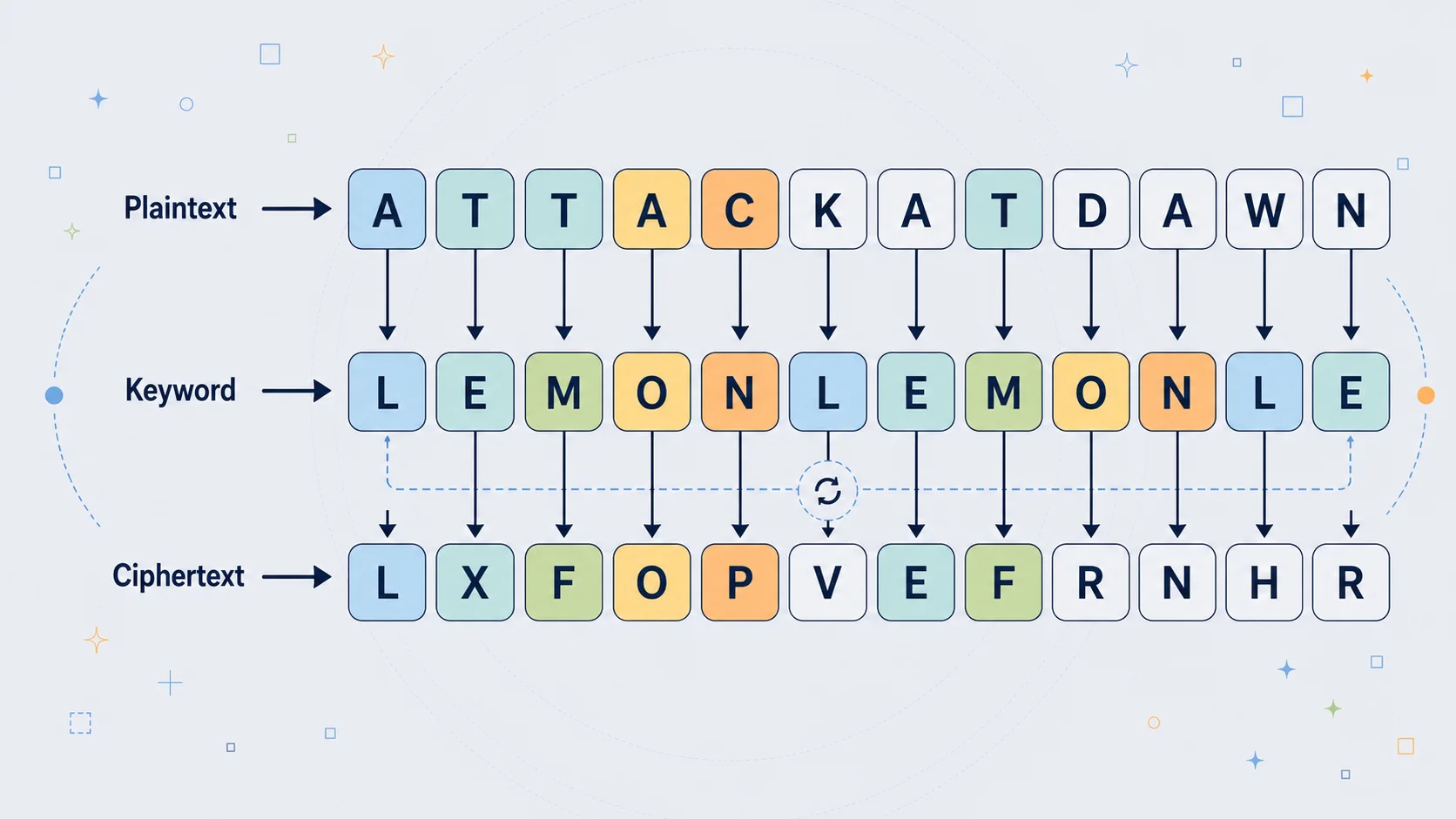
Plaintext: ATTACKATDAWN
Keyword: LEMON
Now repeat the keyword so that it lines up with the plaintext:
Plaintext: A T T A C K A T D A W N
Key: L E M O N L E M O N L E
Using A = 0, B = 1, ..., Z = 25, the Vigenère cipher works by adding the key value to the plaintext value modulo 26.
Rather than writing out every step in full, it is clearer to see the method in the first few letters:
| Position | Plaintext | Value | Key | Value | Sum | mod 26 | Ciphertext |
|---|---|---|---|---|---|---|---|
| 1 | A | 0 | L | 11 | 11 | 11 | L |
| 2 | T | 19 | E | 4 | 23 | 23 | X |
| 3 | T | 19 | M | 12 | 31 | 5 | F |
| 4 | A | 0 | O | 14 | 14 | 14 | O |
| 5 | C | 2 | N | 13 | 15 | 15 | P |
| 6 | K | 10 | L | 11 | 21 | 21 | V |
Continuing in the same way for the rest of the message gives:
LXFOPVEFRNHR
This example captures the central idea of the Vigenère cipher. The same plaintext letter does not always produce the same ciphertext letter, because the shift changes with the keyword. An A encrypted under L becomes L, but an A encrypted under O becomes O, and under N it becomes N. That changing alphabet is what made the Vigenère cipher such an important advance over simple monoalphabetic substitution.
The mathematics underneath
Once the visual method is clear, the formal rule is beautifully compact. If plaintext letters are represented by numbers $P_i$, key letters by $K_i$, and ciphertext letters by $C_i$, then encryption is:
$$ C_i = (P_i + K_i) \bmod 26 $$
and decryption is:
$$ P_i = (C_i - K_i) \bmod 26 $$
This is just a compressed way of describing the same process shown in the worked example above. Each plaintext letter is turned into a number from 0 to 25, each key letter is turned into a shift value, and the two are combined using arithmetic modulo 26.
For example, suppose the plaintext letter is A and the matching key letter is L. Using A = 0, B = 1, ..., Z = 25, we have:
$$ \begin{aligned} P_i &= 0 \\ K_i &= 11 \end{aligned} $$
So encryption gives:
$$ C_i = (0 + 11) \bmod 26 = 11 $$
and 11 corresponds to L, so the ciphertext letter is L.
Decryption works the same way in reverse. If the ciphertext letter is L, then $C_i = 11$, and with the same key letter L we get:
$$ P_i = (11 - 11) \bmod 26 = 0 $$
which takes us back to A.
The important detail is that the keyword repeats. The key stream is therefore periodic rather than random. That repeated structure is exactly what gives the cipher its extra power over simple substitution, and exactly what eventually gives cryptanalysts a way in.
The real history behind the name
The history is more interesting than the simplified classroom version. The cipher commonly taught under the name "Vigenère" was actually described earlier by Giovan Battista Bellaso in 1553. Blaise de Vigenère, writing in 1586, described a related but stronger autokey method. Over time, his name became attached to the simpler repeating-key system instead. The popular schoolbook version is therefore not quite the same thing as Vigenère's more sophisticated original method.
The cipher also did not emerge in isolation. Leon Battista Alberti had already developed an important early polyalphabetic idea with his cipher disk in the fifteenth century, and Johannes Trithemius contributed the tabula recta tradition that later became central to how the Vigenère system was taught. In that sense, the Vigenère cipher is best understood not as a sudden invention, but as the consolidation of several Renaissance advances: rotating alphabets, keyed shifts, and practical hand encryption.
Why it seemed so formidable
The Vigenère cipher was attractive because it attacked the biggest weakness of monoalphabetic substitution directly. If you encrypt an entire message with one alphabet, the statistical profile of the language still comes through strongly enough for frequency analysis to bite. A repeating-key polyalphabetic cipher spreads the plaintext across several Caesar shifts instead. The ciphertext can look noticeably flatter and less revealing than the output of a simple substitution cipher. That flattening is one reason the system acquired its famous aura of strength.
This reputation eventually became so strong that the system was celebrated as le chiffre indéchiffrable, the indecipherable cipher. That title was exaggerated, but historically understandable. For a long time, the Vigenère cipher resisted the most familiar attacks, and even well-read writers praised it long after better cryptanalysis had exposed its weakness.
It also had a practical advantage: it required no machinery, only a memorized key and an agreed method. That portability mattered in diplomatic and military settings. The system, or close relatives of it, did see real historical use, including in the nineteenth century, though practice often fell short of theory because people reused predictable keys or chose weak key phrases. As so often in cryptography, the human element was as important as the mathematics.
What it is not
The Vigenère cipher is sometimes mistaken for a kind of primitive block cipher because the key repeats in cycles. That is misleading. It is not a block cipher in the sense of the Hill cipher or modern block systems. In Vigenère, each plaintext letter influences only its own corresponding ciphertext letter. Change one letter in the input and only one letter changes in the output.
That difference matters because it explains why the cipher can be pulled apart statistically. Once the repeating pattern of the key has been discovered, the ciphertext separates into several independent Caesar-like streams rather than one genuinely entangled transformation.
Where the weakness enters
The Vigenère cipher's strength comes from using several alphabets. Its weakness comes from using them in a repeating cycle. If the keyword is short, the same shifts recur again and again. That recurrence leaves fingerprints in the ciphertext. Once a codebreaker figures out the length of the keyword, the apparently complicated system becomes much more manageable: the ciphertext can be split into columns, one for each key position, and each column behaves like a simple Caesar cipher.
This is why the Vigenère cipher defeats naive frequency analysis but not all frequency analysis. Looking at the whole ciphertext at once blends together several shifted alphabets and muddies the signal. But once letters are sorted by position modulo the key length, the old statistical structure begins to reappear. The language was never destroyed. It was only distributed across interleaved streams.
How it is broken
The classical route into the cipher is to estimate the key length first. The best-known published breakthrough came from Friedrich Kasiski in the early 1860s, usually cited as 1863. Kasiski observed that if repeated pieces of plaintext happen to be encrypted under the same stretch of the repeating key, they produce repeated chunks of ciphertext. The distances between those repeated chunks often share factors with the key length. That is the logic of the Kasiski examination: find repeated ciphertext fragments, measure the gaps between them, and look for common divisors.
A second important route is the index of coincidence, associated with William F. Friedman in the early twentieth century. Natural language does not distribute letters evenly, so English text has a higher coincidence profile than random noise. When a Vigenère ciphertext is arranged into the correct number of columns, each column begins to resemble a monoalphabetic encryption of ordinary language, and the coincidence signal rises. That gives the cryptanalyst another way to estimate the period of the key.
Once the key length is known, the rest is often a matter of patient analysis. Write the message into columns. Each column has been encrypted with one fixed shift. Solve each column as a Caesar cipher, recover the shifts, reconstruct the keyword, and then decrypt the full text. What once seemed like a mysterious polyalphabetic system turns out to be several simple substitution problems wearing one coat.
Relatives and descendants
The Vigenère cipher sits inside a wider family of related systems.
The Caesar cipher is the obvious ancestor: one fixed shift for the whole message. Vigenère can be understood as many Caesar ciphers coordinated by a key.
The Trithemius cipher uses a changing alphabet sequence too, but the sequence is fixed and predictable rather than controlled by a secret keyword. It is an important conceptual precursor.
The autokey cipher is historically closer to what Blaise de Vigenère himself described. Instead of repeating a short keyword forever, it extends the key with plaintext, which removes the obvious periodic repetition that makes the standard classroom version vulnerable.
The running-key cipher pushes the same idea further by using a long nonrepeating text as the key. This makes period-finding attacks harder, although it creates other problems if the running key text is predictable.
The Gronsfeld cipher is a simplified relative that uses digits rather than letters as key values, making it easier to operate but usually weaker in practice.
At the far extreme lies the one-time pad. If the key is truly random, at least as long as the message, never reused, and kept secret, then the same additive structure becomes theoretically unbreakable. At that point, however, the security comes from the random one-time key, not from the classical repeating-key Vigenère system.
There is also a neat algebraic lesson hidden here. Encrypting with one Vigenère key and then encrypting again with another does not usually create a whole new species of cipher. Because the shifts add modulo 26, double encryption collapses to a single effective Vigenère-style system, with the overall pattern governed by the relationship between the two key lengths. Simply layering weak systems does not automatically produce a strong one.
Why it still matters
No one should use the classical repeating-key Vigenère cipher to protect real secrets today. Its importance now is educational and historical rather than practical. It marks a moment when cryptography stopped feeling like a collection of letter tricks and began confronting deeper issues: key schedules, periodicity, statistical leakage, and the difference between an algorithm and a secret key.
It also teaches one of the most enduring lessons in the subject: defeating the most obvious attack is not the same thing as being secure. The Vigenère cipher looked formidable because it broke the simplest form of frequency analysis. But once better methods emerged, its hidden regularities became visible. That lesson still echoes through modern cryptography, where repetition, structure, and poor key handling remain dangerous long after a system begins to look sophisticated.
For learners, it remains close to ideal. It is simple enough to do by hand, rich enough to support real cryptanalysis, and historically important enough to show how classical ciphers gradually opened into deeper mathematical thinking. It stands right on the threshold: beyond simple substitution, but not beyond statistics; more subtle than Caesar, but still very far from modern cryptographic security.
A simple Python implementation
Here is a clean version in Python that preserves spaces and punctuation but only shifts ASCII letters A-Z. That small restriction avoids the Unicode edge cases that come from Python's broader isalpha() behavior. Python's str.isalpha() follows Unicode character properties, so an ASCII-only classical cipher tool is usually better off checking explicitly for English letters.
Python exampleShow code
def clean_key(key):
key = ''.join(ch.upper() for ch in key if 'A' <= ch.upper() <= 'Z')
if not key:
raise ValueError("Key must contain at least one ASCII letter A-Z.")
return key
def vigenere_encrypt(text, key):
key = clean_key(key)
result = []
key_index = 0
for ch in text:
if 'A' <= ch <= 'Z' or 'a' <= ch <= 'z':
shift = ord(key[key_index % len(key)]) - ord('A')
base = ord('A') if ch.isupper() else ord('a')
encrypted = chr((ord(ch) - base + shift) % 26 + base)
result.append(encrypted)
key_index += 1
else:
result.append(ch)
return ''.join(result)
def vigenere_decrypt(text, key):
key = clean_key(key)
result = []
key_index = 0
for ch in text:
if 'A' <= ch <= 'Z' or 'a' <= ch <= 'z':
shift = ord(key[key_index % len(key)]) - ord('A')
base = ord('A') if ch.isupper() else ord('a')
decrypted = chr((ord(ch) - base - shift) % 26 + base)
result.append(decrypted)
key_index += 1
else:
result.append(ch)
return ''.join(result)
plaintext = "Attack at dawn!"
key = "LEMON"
ciphertext = vigenere_encrypt(plaintext, key)
recovered = vigenere_decrypt(ciphertext, key)
print("Plaintext :", plaintext)
print("Key :", key)
print("Ciphertext:", ciphertext)
print("Recovered :", recovered)
What the code is doing
The program follows the mathematical rule exactly:
- Each key letter becomes a shift from
0to25. - Encryption adds that shift modulo 26.
- Decryption subtracts it modulo 26.
- Spaces and punctuation are preserved.
- The key advances only when a letter is actually processed.
That last point is a modern design choice, but usually the right one for a readable website tool. If punctuation consumed key characters, the alignment of the key would become awkward and implementation-dependent.
Closing thought
The Vigenère cipher is one of the most revealing systems in classical cryptography because it is strong enough to feel ingenious and weak enough to be broken elegantly. It stands at an intellectually fascinating point in the history of the subject: beyond the simplicity of Caesar, but still exposed to statistics; more advanced than ordinary substitution, but nowhere near the security standards of modern cryptography.
That is why it still deserves attention. Not because it can protect secrets today, but because it teaches, in a compact and memorable form, one of the deepest truths in the field:
Security is not the same thing as looking complicated.