The Hill cipher stands at the point where classical cryptography starts to feel unmistakably mathematical. It still belongs to the world of hand ciphers, alphabets, and modular arithmetic, but its central idea is different: encrypt blocks of letters together by treating them as vectors and multiplying them by a key matrix.
When a Cipher Stops Being a Word Game
The Hill cipher stands out from most classical ciphers because it does not work by nudging one letter at a time around the alphabet. Instead, it converts letters into numbers, groups them into blocks, and transforms those blocks with matrix multiplication. That makes it one of the clearest examples of a polygraphic substitution cipher: a cipher that encrypts several symbols together rather than independently.
Lester S. Hill introduced the idea in 1929 in Cryptography in an Algebraic Alphabet, and the cipher is still remembered because it brought explicit linear algebra into practical cipher design in a way older hand ciphers had not.
That shift matters. A Caesar cipher, an Affine cipher, or a simple substitution cipher acts on single letters, so the structure of the plaintext leaks more easily into the ciphertext. The Hill cipher instead mixes letters together inside each block. One letter can influence several ciphertext symbols at once. That does not make it secure by modern standards, but it does make it a major conceptual step beyond simple alphabet tricks.
From Alphabet to Arithmetic
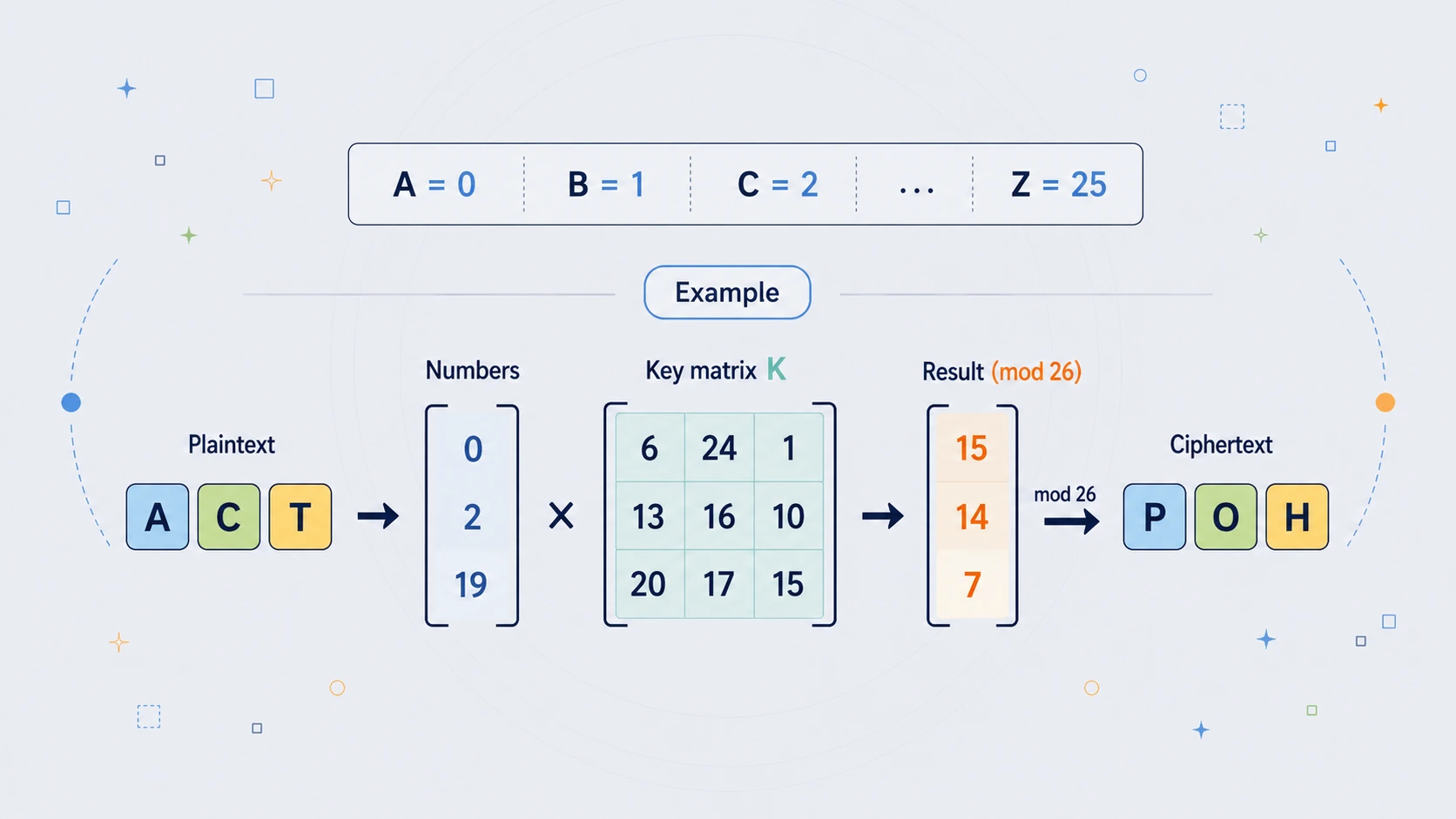
In the standard classical version, the Hill cipher uses the 26-letter alphabet and assigns each letter a number:
A = 0
B = 1
C = 2
...
Z = 25
All arithmetic is then done modulo 26. A plaintext message is split into equal-sized blocks, and the block size depends on the size of the key matrix. A $2 \times 2$ key works on pairs of letters, a $3 \times 3$ key works on groups of three, and so on. Each block is treated as a column vector, multiplied by the key matrix, and reduced modulo 26 to produce the ciphertext block.
This is the essential insight of the cipher: encryption becomes a mathematical transformation. The plaintext is no longer shifted or substituted in the ordinary single-letter sense. It is mapped into vectors and pushed through a matrix. That is why the Hill cipher feels more modern than many of its contemporaries.
The Core Encryption Rule
The rule for encryption is compact:
$$ C = K \cdot P \pmod{26} $$
where:
- $P$ is the plaintext vector
- $K$ is the key matrix
- $C$ is the ciphertext vector
For a $3 \times 3$ Hill cipher, one famous example uses the key matrix:
$$ K = \begin{pmatrix} 6 & 24 & 1 \\ 13 & 16 & 10 \\ 20 & 17 & 15 \end{pmatrix} $$
The plaintext block ACT becomes:
$$ \begin{pmatrix} 0 \\ 2 \\ 19 \end{pmatrix} $$
because A = 0, C = 2, and T = 19. Multiplying and reducing modulo 26 gives:
$$ K \begin{pmatrix} 0 \\ 2 \\ 19 \end{pmatrix} = \begin{pmatrix} 67 \\ 222 \\ 319 \end{pmatrix} \equiv \begin{pmatrix} 15 \\ 14 \\ 7 \end{pmatrix} \pmod{26} $$
Those numbers correspond to:
15 14 7 -> P O H
ACT -> POH
That example is famous for a reason: it shows, in one compact calculation, what makes the Hill cipher special. The plaintext block is not disguised by a letter-by-letter mapping. It is transformed as a unit.
Why the Cipher Feels Clever
One of the most interesting things about the Hill cipher is that a small change in the plaintext can alter the whole ciphertext block. With the same $3 \times 3$ key above:
ACT -> POH
CAT -> FIN
That is an early illustration of diffusion: the influence of the plaintext is spread across the output. The Hill cipher does not create modern security, but it does create a more thoroughly mixed ciphertext than a simple monoalphabetic substitution. This is one reason it feels like a bridge between classical ciphers and later block-cipher ideas.
It is worth being precise here. The Hill cipher did not solve cryptanalysis, and it did not make frequency analysis irrelevant in every sense. What it did do was make simple single-letter frequency analysis far less effective, because the cipher no longer substitutes one plaintext letter for one ciphertext letter in a stable way.
The Key Must Be a Valid Matrix
This is the first place where the Hill cipher becomes unmistakably mathematical: not every matrix can be used as a key.
To decrypt a Hill ciphertext, the receiver must multiply by the inverse of the key matrix. That means the key matrix has to be invertible modulo 26. In practice, that requires its determinant to be coprime with 26. Since $26 = 2 \times 13$, the determinant cannot be 0 modulo 26, divisible by 2 modulo 26, or divisible by 13 modulo 26. If it shares a factor with 26, the matrix has no modular inverse and decryption fails.
That requirement is not an optional technicality. It is one of the defining rules of the cipher. A key is not merely a secret word or phrase; it must generate a matrix that can actually be reversed. That is why Hill cipher implementations always need a determinant check.
A Worked 2 x 2 Example
A smaller example shows the mechanics more clearly. Take the key:
$$ K = \begin{pmatrix} 3 & 3 \\ 2 & 5 \end{pmatrix} $$
and encrypt the plaintext HELP. Converting letters into numbers gives:
H = 7
E = 4
L = 11
P = 15
So the plaintext becomes two vectors:
$$ \begin{pmatrix} 7 \\ 4 \end{pmatrix}, \quad \begin{pmatrix} 11 \\ 15 \end{pmatrix} $$
Encrypting the first pair gives:
$$ \begin{pmatrix} 3 & 3 \\ 2 & 5 \end{pmatrix} \begin{pmatrix} 7 \\ 4 \end{pmatrix} = \begin{pmatrix} 33 \\ 34 \end{pmatrix} \equiv \begin{pmatrix} 7 \\ 8 \end{pmatrix} \pmod{26} $$
which becomes HI. Encrypting the second pair gives:
$$ \begin{pmatrix} 3 & 3 \\ 2 & 5 \end{pmatrix} \begin{pmatrix} 11 \\ 15 \end{pmatrix} = \begin{pmatrix} 78 \\ 97 \end{pmatrix} \equiv \begin{pmatrix} 0 \\ 19 \end{pmatrix} \pmod{26} $$
which becomes AT. So the full encryption is:
HELP -> HIAT
That result looks strange at first, but that is part of the point. The ciphertext is not trying to resemble the original word. It is the output of a reversible mathematical transformation.
How Decryption Works
Decryption uses exactly the same idea in reverse:
$$ P = K^{-1} \cdot C \pmod{26} $$
For the $2 \times 2$ example above, the inverse matrix is:
$$ K^{-1} = \begin{pmatrix} 15 & 17 \\ 20 & 9 \end{pmatrix} \pmod{26} $$
Multiplying the ciphertext blocks of HIAT by that inverse matrix returns HE and LP, restoring the original plaintext HELP. This symmetry is one of the most elegant parts of the Hill cipher: encryption is multiplication by the key matrix, and decryption is multiplication by its modular inverse.
Why It Mattered Historically
Hill introduced the cipher in 1929, and later work around the idea included a mechanical implementation. A patent associated with Hill and Louis Weisner described a cryptographic device for carrying out the transformation mechanically, and later descriptions refer to a $6 \times 6$ Hill-style machine using gears and chains. That shows how seriously the idea was taken: this was not just a blackboard curiosity, but an attempt to build algebraic encryption into an actual apparatus.
The Hill cipher was important because it demonstrated three things clearly. First, encryption could operate on blocks rather than individual letters. Second, a cipher could be designed to create diffusion rather than only substitution. Third, serious mathematics, especially matrix algebra and modular inverses, could sit at the centre of a practical cipher system.
Where It Falls Short
For all its elegance, the basic Hill cipher has a fatal weakness: it is completely linear. That means an attacker who knows enough plaintext and ciphertext pairs can set up a linear system and solve directly for the key matrix. In general, an $n \times n$ Hill cipher can often be broken with about $n^2$ known plaintext characters arranged into enough independent blocks. That makes the cipher highly vulnerable to a known-plaintext attack.
So the Hill cipher is a strange mixture of sophistication and fragility. It is mathematically richer than most classical hand ciphers, yet fundamentally too linear to resist modern-style cryptanalysis. Its beauty lies more in its structure than in its security.
Its Link to Modern Cryptography
The Hill cipher is not secure enough for real modern secrecy, but one of its core ideas survives: matrix-based mixing can be useful for diffusion. That is why the Hill cipher still gets mentioned in discussions of modern cryptographic design. NIST's AES specification describes MixColumns as a transformation that mixes the data within each column of the state, and that operation is expressed as a matrix multiplication over a finite field.
The Hill cipher is not AES, of course, but the family resemblance is real: controlled algebraic mixing remains a powerful design tool when combined with strong nonlinear components.
That distinction is important. The Hill cipher has diffusion, but it does not have the nonlinear machinery that gives modern ciphers their real strength. In that sense, it is better understood as an ancestor of later ideas than as a secure system in its own right.
A Note on Variants
The classical Hill cipher uses the 26-letter alphabet and works modulo 26. But many classroom versions enlarge the alphabet to include spaces, punctuation, digits, or underscores. Some course materials use a prime-sized alphabet such as 29 or 41 symbols, because working modulo a prime avoids some invertibility headaches. That is a perfectly sensible educational adaptation, but it is still a variant rather than the standard historical form.
A Simple Python Example
Here is a clean $2 \times 2$ Python example that both encrypts and decrypts, while also checking that the key matrix is valid:
Python exampleShow code
def clean_text(text):
return "".join(ch for ch in text.upper() if ch.isalpha())
def text_to_numbers(text):
return [ord(ch) - ord("A") for ch in text]
def numbers_to_text(nums):
return "".join(chr(n + ord("A")) for n in nums)
def mod_inverse(a, m):
a %= m
for x in range(1, m):
if (a * x) % m == 1:
return x
raise ValueError("No modular inverse exists.")
def determinant_2x2(matrix):
return matrix[0][0] * matrix[1][1] - matrix[0][1] * matrix[1][0]
def inverse_key_2x2(matrix, mod=26):
a, b = matrix[0]
c, d = matrix[1]
det = determinant_2x2(matrix) % mod
det_inv = mod_inverse(det, mod)
# Adjugate matrix for 2x2.
adj = [
[ d, -b],
[-c, a]
]
return [
[(det_inv * adj[0][0]) % mod, (det_inv * adj[0][1]) % mod],
[(det_inv * adj[1][0]) % mod, (det_inv * adj[1][1]) % mod],
]
def multiply_matrix_vector(matrix, vector, mod=26):
return [
sum(matrix[0][i] * vector[i] for i in range(2)) % mod,
sum(matrix[1][i] * vector[i] for i in range(2)) % mod,
]
def hill_encrypt_2x2(plaintext, key_matrix):
text = clean_text(plaintext)
nums = text_to_numbers(text)
if len(nums) % 2 != 0:
nums.append(ord("X") - ord("A"))
out = []
for i in range(0, len(nums), 2):
block = nums[i:i+2]
out.extend(multiply_matrix_vector(key_matrix, block))
return numbers_to_text(out)
def hill_decrypt_2x2(ciphertext, key_matrix):
inv_key = inverse_key_2x2(key_matrix, 26)
nums = text_to_numbers(clean_text(ciphertext))
if len(nums) % 2 != 0:
raise ValueError("Ciphertext length must be even for 2x2 decryption.")
out = []
for i in range(0, len(nums), 2):
block = nums[i:i+2]
out.extend(multiply_matrix_vector(inv_key, block))
return numbers_to_text(out)
# Example key:
# [3 3]
# [2 5]
key = [
[3, 3],
[2, 5]
]
plaintext = "HELP"
ciphertext = hill_encrypt_2x2(plaintext, key)
recovered = hill_decrypt_2x2(ciphertext, key)
print("Plaintext :", plaintext)
print("Ciphertext:", ciphertext)
print("Decrypted :", recovered)
With the example key above, this produces:
Plaintext : HELP
Ciphertext: HIAT
Decrypted : HELP
This code is doing exactly what the hand method does. It converts letters to numbers, processes the message in pairs, multiplies each pair by the key matrix modulo 26, and then uses the inverse matrix for decryption. The important extra step is the determinant check hidden inside inverse_key_2x2(): if the determinant has no modular inverse modulo 26, the key is invalid and the program stops. That is not a programming detail; it is one of the core mathematical rules of the cipher.
Why the Hill Cipher Still Deserves a Place
The Hill cipher still matters because it teaches something larger than itself. It shows that cryptography is not just about sneaky alphabets or puzzle-book tricks. It is about structure, reversibility, controlled mixing, and mathematical constraints. It also shows a deeper lesson: diffusion alone is not enough. A cipher can look elegant, clever, and sophisticated, yet still be breakable if its internal structure is too linear.
That is why the Hill cipher remains such a good subject for a serious classical-cipher page. Historically, it is important. Mathematically, it is beautiful. Educationally, it is one of the best gateways from old ciphers to modern cryptographic thinking.